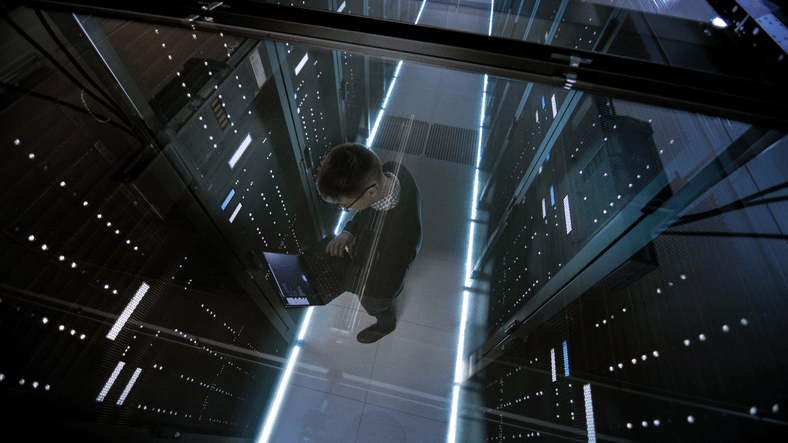
Over the years, businesses’ mission-critical technology has expanded at a rapid pace. A network no longer consists of only servers, client computers, and basic networking equipment. Cloud computing has been introduced to host “X as a Service” solutions and applications that rely on big data, allow mobile and remote endpoints, network shares, and multiple communication applications, just to name a few. Even the solutions meant to secure the network and endpoints have grown complex to the point where a misconfigured security solution could leave an organization vulnerable.
This is why many organizations turn to outside partners to conduct a network security assessment. Having one performed by a trusted partner lets you know not only where your organization's security posture currently stands, but also what you can do to better protect yourself from the current threat landscape.