
When it comes to F5 BIG-IP and specifically F5 LTM products it can be easy to think of them as a mechanism for load balancing traffic and nothing more. What can be overlooked is that these devices are highly intelligent and offer a diverse range of ways with which you can optimize your traffic and further protect your network.
Making the most of these capabilities can help ensure you are able to manage your network in the most secure and efficient manner possible. The truth is that whether you have an F5 in your environment already or if you are considering adding them to your arsenal, it is important to understand the full capabilities that they offer. One way that you can greatly increase the capabilities of an F5 Big-IP and in turn increase security and efficiency for the traffic that its processing is to utilize their SSL offloading capabilities.
SSL requirements are continuing to increase as more and more as websites and applications push for increased security. As of September of 2018 more than one-half of most visited websites world-wide actively re-direct to https by default. This trend show these numbers continuing to climb as more and more companies recognize the necessity of encrypting user’s traffic. Traditionally as ssl re-equipments increase so does the resource cost of managing individual connections for application servers.
Along with the resource considerations, in today’s day and age of ‘SSL everywhere’ it can be difficult to maintain visibility into the application layer data on devices other than the servers doing SSL decryption. In the most standard environments, F5 https virtual servers will receive an incoming ssl connection, complete the tcp handshake, make a load balancing decision, and then forward everything above layer 4 along for the server to deal with. While this method does ensure end to end encryption, its places the majority of the load on your servers and it negates the ability of you BIG-IP from being involved in layers 5 through 7. Inspection, decision making, and traffic modifications above the transport layer cannot be preformed by the BIG-IP because it doesn’t have access to any of the encrypted data. Additionally, this configuration allows clients an additional layer of direct connection to the server they are accessing.
If our goal is to manage a highly secure network in the most efficient way possible then we should consider alternatives to the typical design where application servers are solely responsible for maintaining SSL sessions. We should also consider the benefits of separating a direct session layer connection between client and sever, especially when we have a device readily capable of and designed for doing so.
What is SSL Offloading?
SSL offloading is the process of configuring your BIG-IP to act as an SSL server for SSL encrypted client connections. With SSL offloading configured, Incoming SSL traffic is handled directly by the BIG-IP where it previously would have been passed off to the backend servers. With the necessary SSL certificate and private key imported on an F5 device and applied to an SSL profile, SSL termination can be preformed by your F5 itself. From here the options are two fold:
- True offloading of SSL. In this scenario clients communicate with your F5 virtual server over an encrypted session just as they would have done with the application server previously. The server-side connection proceeds over plaintext meaning there is no SSL encryption when it comes to the connection between your F5 and the application server. The obvious benefit here is that the application servers are relieved of the expensive processing requirements that come along with managing SSL sessions. F5 devices are designed with SSL offloading in mind and the crypto cards allow hardware to accelerate SSL transactions rather than using valuable CPU cycles. Application servers save resources that can instead be used to handle additional connections more efficiently.
- SSL bridging, also known as SSL re-encryption. With this method, the F5 will act as an SSL server on the client side, allowing it access to application data, but when it comes time to establish connections with the application servers, it will act as an SSL client, re-encrypting the traffic. In many environments, this is likely the preferred method as you enable application traffic inspection and modification(on your F5), and adding an additional layer of security(by establishing a second secure connection to your server) while maintaining end to end encryption. Additionally, you can do things such as use a larger(more resource intensive) key on the client-side of the big-ip, where security requirements are more stringent, and re-encrypting with a smaller key on the server-side, thus still offering some relief to your servers.
What are the Benefits of Offloading SSL?
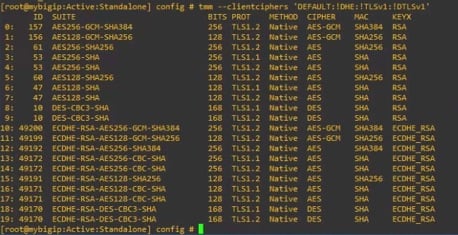
Centralized management of your SSL certificates, private keys, and general SSL configuration including cipher suites, compatible protocol versions and protocol options. In an environment with numerous secure applications, managing all of the SSL requirements on an application to application basis is doable but very likely not the most efficient manner. From storing your certs and keys in a centralized location, to configuring client authentication in one place(rather than on each server individually), to configuring a cipher string once and applying it across the board, there is no question that F5 is able to offer an ease of use and efficiency that you may not have previously considered.
In addition to the security benefits touched upon further below, SSL offloading provides the opportunity to save valuable resources on application servers by allowing you’re BIG-IP to handle the work. The resources saved can add up in a big way when you consider the overhead of establishing and maintaining SSL connections. Offloading or Re-encrypting SSL can allow you to configure your network in way that allows you to get the most out of your F5 as well as the devices for which it is preforming application delivery for.
When SSL decryption is preformed by an F5, as opposed to by your application server, you also remove a layer of direct communication between clients and servers. Clients no longer have session layer access to your server and with this in place, your server no longer needs to be the first and only device to inspect application layer requests. With the F5 decrypting SSL, it enables a plethora of security and optimization abilities for which BIG-IP products are designed. Let’s look at just a few of these abilities:
- Additional Persistence Methods. With many applications, ensuring a client persists to the same webserver for each of its requests is a critical aspect. With access to the encrypted data your F5 can make far more intelligent persistent load balancing decisions using tools such as SSL session id, HTTP cookies as well as customizable tcl expressions which allow you to create a persistence record based on just about any piece of network traffic desired(this is known as universal persistence.)
- iRules. F5 BIG-IP iRules are scripts written in TCL which execute against network traffic passing through your F5 in real time. From simple to complex, the value of iRules comes with endless possibilities and customization which can be tweaked to meet your exact and specific needs. For one of the most basic examples consider the following scenario: An HTTPS request is received by an F5 virtual server, SSL is decrypted and an iRule is processed against the request. The logic of the iRule states; if this request url contains ‘non-default’ then send the traffic to the non-default server pool, otherwise send this traffic to the default pool. This is truly one of the most basic examples but it showcases a scenario where a simple 8 line piece of TCL code could help optimize the flow in your network or solve a design issue in a very efficient manner. iRules also offer an excellent manner of logging application layer data points that you may be interested in. This may offer solutions to better understand your traffic, further secure your network, or meet your analytics needs.
- HTTP Profiles. F5 HTTP profiles which are required for HTTP inspection and cannot be applied unless decryption occurs are the F5s default method of inspecting and modifying HTTP traffic. The enforcement options within the profile offer many additional security options. Some basic examples of what an HTTP profile can offer include things like, allowing and disallowing specific HTTP request methods, inserting the true client IP address for the servers use(X-Forwarded-For), encryption of HTTP cookies, just to name a few.
- One Connect Profiles. One Connect Profiles are a configuration object designed to save your servers additional resources by re-using server-side TCP connections in conjunction with HTTP keep-alives. In situations where multiple clients have connected to a virtual server, and load balancing decisions have been made for each(sending them to the same server), these connections can be sent over the same server-side TCP stream. This can significantly reduce load on your server as it avoids the server from constantly needing to establish and re-establish TCP sessions and drastically reduces the overall number of TCP sessions being managed on your server.
- Web Acceleration and Compression Profiles. With access to application data F5 BIG-IPs are capable of caching and compressing data which can further relieve your web servers of load. These profiles can be configured to cache a server’s response for a specified amount of time and respond directly to clients throughout the time that content is cached. Additionally, http compression can be preformed right on the BIG-IP.
- Additional Modules. If you are considering using or if you are already utilizing additional F5 modules such as ASM(Application Security Manager) or APM(Access Policy Manager) than decrypting ssl will be necessary to allow you to use these products to their full potential as well. The security enhancements these modules can provide are quite drastic and well worth consideration.
Although this list is by no means exhaustive, we’ve touched on some of the ways that you can make the most of your F5 BIG-IP products now and in the future. It can be easy to think of these products as simply load balancers but, as hopefully you’ve seen here, there are so many more capabilities which they can provide. Whether this applies to devices in your data center today or those that you may be considering in the future it is important to know the full value of these products.
For additional information regarding any of the topics mentioned, I highly suggest checking out the community user database available at devcentral.f5.com as well as the F5 knowledge base which is available at askf5.com.




Comments